
At 4 am on a muggy, dim night in central Indiana, a dozen troopers, detectives, and investigators arrive at a house with a search warrant. Nothing about the house is much different from the hundreds of other houses the team has searched. Sometimes they’re clean. Sometimes they’re filthy drug dens. Sometimes they’re empty, and sometimes the residents answer the door.

At this house, investigators comb through looking for computers, tablets, phones, and tiny disks and micro SD cards the size of a cereal flake. Amid the rush, anxious kids emerge from their bedrooms. The team needs help and calls for Hunter, the electronic scent-detection K9.
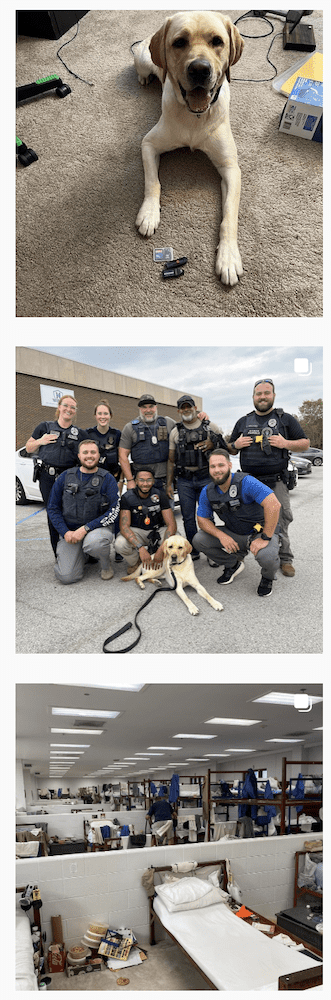
Hunter, a three-and-a-half-year-old yellow labrador, has two jobs at this house: keep everyone calm and help investigators find evidence. Much like arson detection dogs sniff for accelerants like gasoline, Hunter can smell a compound called triphenylphosphine oxide (TPPO) — even through drywall. TPPO covers the circuit boards in all storage devices, from large hard drives down to microSD cards, to keep them from overheating.
Indianapolis Metropolitan Police Detective Darin Odier brings Hunter into the home. Within ten minutes, Hunter indicates toward a single box in a room stacked with boxes. Inside, the box has SD cards and thumb drives with hundreds of gigabytes of data. Det. Odier recognizes, “It’s easy for us to miss this stuff. One of our biggest issues on a search warrant is ‘Did we get it all? Did we miss it?”
Hunter is one of only a handful of electronic sniffing canines at work with law enforcement in the United States. Technology scent detection dogs the most highly trained dogs anywhere in law enforcement. Their conditioning includes a rigorous three months of scent training and six months of cumulative training with a handler. Few dogs meet the standards required for service.
Even more challenging is Hunter doesn’t have a food bowl. “He only eats when we train, and he and I train about three times a day.” That means if they’re not conducting a search warrant or get home late after a long day, Det. Odier hides technology in random rooms of his house to train — and feed — Hunter.
The Indiana Crimes Against Children Task Force, which includes Det. Odier and K9 Hunter, the Indiana State Police Crimes Against Children division, the IMPD Cyber Crimes Unit, and federal agencies, deploy Hunter amid search warrants targeting, among other things, child pornography.
“After a search, Hunter plays a vital role in de-escalating kids, calming them down. Then we can go to Susie’s Place, and he continues to be a natural, loving dog,” says Det. Odier. “We’ve had cases where children get through their interview at Susie’s Place holding Hunter, discussing what they need to talk about.” Then, the next day, the team returns to scouring the internet for sexual predators and investigating child pornography.
Child sexual abuse material “is currency”
“Back in 2006 when I started this job, I would literally go into a music chat room to talk about music and these guys would bombard my persona until the conversations came around to sex. It was all driven by them and was like fish in a barrel,” recalls Det. Odier, now in his 33rd year in law enforcement, 16 of which is in the cyber crimes space. “Today, we don’t have the time or the power to be that proactive.”
Technology has changed since 2006 when Det. Odier started online. With phones and the proliferation of the internet to virtually every breathing person in the United States, the job is massive.
Predators have evolved, too. “The best child predators are extremely difficult to catch. They’re on the dark web, but we’re not focused on them. We’re focused on people actively seeking sexual contact with kids,” says Det. Odier.
The dark web uses the same internet you’re familiar with, but text, videos, and images exist on “darknets” — special overlay networks that use the internet but require specific software, configurations, or authorization to access. If you remember using Napster or Limewire in the early 2000s, services akin to those power the dark web today.
“A 28-year-old man who really likes 14-year-old girls goes online pretending to be 17, they form a relationship, they meet, and the child is in over their heads. Or, it doesn’t even come to sexual contact. It’s content, like videos and photos. If guys can get that online, especially something unique —like material involving 3 or 4-year-olds — stuff that almost no one in the world has — that’s currency,” says Det. Odier. “They can trade those videos with other people for the stuff they do like.”
See more on Hunter’s Instagram
Det. Odier estimates their cases are about 70% men seeking material of young girls, with 30% seeking boys. “Women are involved, too, sometimes in conjunction with an adult male.” The factors leading to this scenario are complex and tragically human.
According to Det. Odier, “One example is a man and a woman lose some of their passion in a marriage. Dad broaches the subject of a young girl, and mom kinda plays along with it until it ends up as hands-on contact. Or, maybe both of them are recording it, or mom gave dad access to the child.”
Everyone at Susie’s Place is “there for the right reasons”

Because cyber crimes almost always involve many jurisdictions with servers and digital material spread across the world, internet crimes are usually prosecuted at the federal level. Indiana sits in two federal districts. Indiana’s southern federal district — which includes Indianapolis and all points south of about Interstate 70 to the state line — is one of the smallest in the country. “But last year we were #2 in the U.S. for federal exploitation cases filed,” says Det. Odier. “It doesn’t mean we necessarily have the most crime, but it does mean we have an effective task force.
“We always say we investigate the evil that no one wants to acknowledge occurs. We don’t want to think other humans can do this. But in addition to online crimes, we do a lot of work where a child makes a disclosure that their dad or a stepdad is molesting, and we find a hidden camera recording it. That’s where it moves from child molesting to child pornography. That’s also where our connection with Susie’s Place comes in,” says Det. Odier.
“Every person at Susie’s Place is there for the right reasons. We’re not just there for the forensic interview. They are the middle letter of CAC — Advocacy. It’s truly what they do. They’re there to provide resources to the child and family, whether that’s through social work or counseling,” says Det. Odier.
He adds, “We work together as partners throughout the process, which is the best way to do our investigations, and it’s best for the children. I know I can phone whoever is on-call at 4 am and they’ll say they’ll be there in 20 minutes. They do whatever needs to be done, above and beyond every single time.”
“These cases involve the worst stuff on the internet, and we look at it all day long,” says Det. Odier. Everyone in the task force and at Susie’s Place leans on Hunter for a break. “It’s nice knowing we can go outside with him, throw a ball, or just pet him,” he adds.
“It’s incumbent on us as parents to be nosy”
Det. Odier has two daughters, 17 and 23. “For the last ten years, my wife and I lived through this with our daughters online. Just because I’m in this job doesn’t mean they can’t be victims,” he says. “It’s terrifying and disgusting.”
“It is incumbent on us as parents to be nosy. The world is so different now — children can make life-changing impactful mistakes with a click of a button like that,” he says, snapping his fingers. “If parents aren’t in tune with what they’re doing, we’re setting them up to be victims.”
Tips for working with your kids’ devices
Always know your child’s passcodes, PINs, and device unlocks.
“If a parent doesn’t know a kid’s passcode, it makes steam come out of my ears,” says Det. Odier. “Parents are paying for it, if they’re locking you out there’s a reason for it.”
Use parental controls to prohibit all app downloads without your consent.
“My kids were never allowed to download an app without my permission. Unless I had an investigation, they were often so new I wanted to research to find what they could or couldn’t do.”
Read more about tech tips for parents at the Indiana Chapter of NCA
Demand to see their devices, unlocked, in an instant and know what apps they’re using and their profile names.
“My kids also knew if I wanted to see their phone, they basically had to run to give it to me. There’s no time to delete stuff.
Build a relationship of trust and protection.
“The most important thing is we have to have relationships with our kids so they know if they make a mistake they can come to us. If they’re in too deep, they have to be able to come to mom and dad or a police officer — someone they can trust. Otherwise, they get in deeper.”


